The landscape of network monitoring tools is vast, offering a multitude of options to choose from. As a result, selecting the most suitable tool is no straightforward task and necessitates careful research and analysis. In this post, we provide guidance to help you identify the best network monitoring solutions for your enterprise network. We’ll go over the following sections:
- Benefits of network monitoring
- Type of network monitoring tools
- Competitive analysis
- NetBeez network monitoring
Network Monitoring Benefits
Network monitoring tools are of vital importance as they empower organizations and IT teams to:
- Proactively Detect Issues: Network monitoring tools continuously interface with your network devices and identify anomalies or performance degradation issues. They help identify potential issues with a computer network as soon as they happen. The proactive approach of network monitoring save organizations several hours of downtime and costly repairs.
- Optimize Network Management: Network monitoring tools highlight critical performance metrics that help tune the network configuration. Metrics like bandwidth available, usage, and traffic patterns allow network administrators to make informed decisions for capacity planning.
- Secure the Network: Security breaches and threats are more common. Organizations need to be prepared by detecting and mitigating such risks. Network monitoring tools solve a critical function of security monitoring.
- Save Costs: Network monitoring helps Network Operations to implement optimizations, proper planning, and reducing troubleshooting costs. Help Desk teams can save costs in support hours by empowering the technicians to gather all the data required to promptly address a customer complaint or request.
Types of Network Monitoring Tools
When selecting the right network monitoring system, consider which tool is appropriate for monitoring a network infrastructure and which one should be used for monitoring the digital experience of end-users. However, before adventuring into the jungle of network monitoring tools, be aware that there are three main categories of network monitoring tools:
- SNMP
- Passive
- Active
Each one of them has a specific function, with associated benefits and limits. Let’s review each one of them in details.
SNMP Monitoring Tools
These network monitoring systems use the SNMP protocol to monitor network devices. The servers, often referred to as SNMP pollers, actively poll the devices’ status and monitor resource consumption, including CPU utilization, memory usage, and data transmitted and received on their interfaces. SNMP tools generate alerts when network components becomes inaccessible or experiences resource overload.
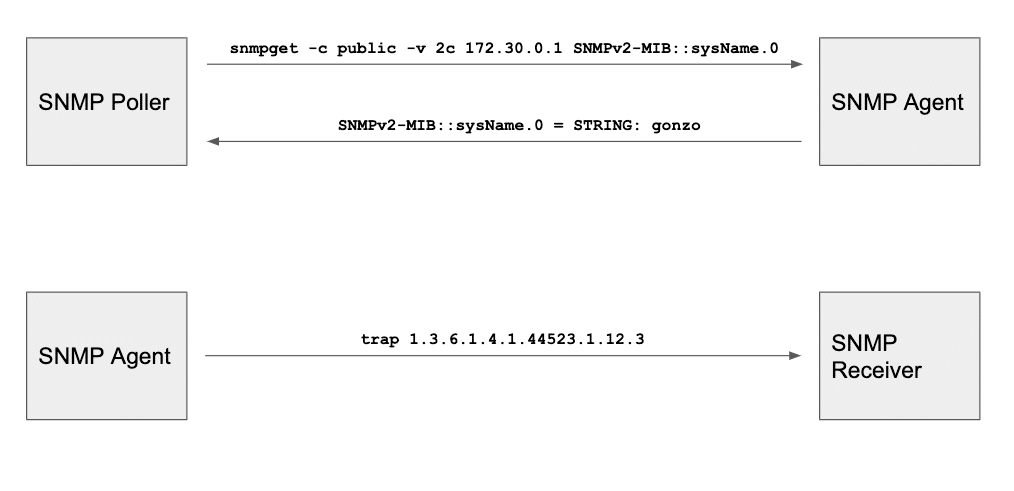
The following picture shows how SNMP works. On the top part an SNMP poller, or server, periodically queries an SNMP agent (monitored device) to gather its status and resources available. In this specific example the poller is requesting the SNMP agent the local machine’s hostname. The SNMP agent returns the hostname as a string (gonzo). This is how SNMP-based servers monitor network elements.
On the bottom, we see a different functionality of SNMP. This time an SNMP agent agent sends an SNMP trap to an SNMP receiver (server) to alert about a failure. This type of transactions enables network components to report that something is wrong to an SNMP server, so it can alert the network administrator.
Passive Network Monitoring Tools
Passive network monitoring systems process and capture real user data (also called traffic flow). These tools generate aggregate traffic monitoring statistics, breaking them down based by protocols and hosts. The network administrator can identify the machines (top talkers) that are consuming the capacity of a specific network. Passive tools can also inspect a specific sequence of packets to pinpoint performance issues between a client and a server.
Passive Monitoring Components
There are three ways to passively monitoring a network: network TAP, SPAN port, and flow-based protocols. Let’s briefly introduce each one of them:
- Network TAPs are dedicated devices that are installed in-line where the traffic has to be analyzed. A network TAP replicates the entire content of the frames (layer 2) flowing across. For this reason, network TAPs are the best option for Deep Packet Inspection (DPI). Many SIEM (Security Information and Event Management) tools adopt this technology to proactively identify and mitigate potential security breaches or attacks.
- SPAN (Switch Port for ANalysis) ports are configured on a switch by sending a copy of the traffic from a specific port or VLAN to another port on the switch itself or on another switch that has been connected to a network collector. SPAN ports are able to copy the entire packet, including its payload.
- Flow analysis by using a protocol either implemented by network hardware vendor, such as NetFlow and s-Flow, or by an open standard such as IPFIX (IP Flow Information Export). This type of passive analysis doesn’t capture the full content of a packet, but just its header, so it’s mostly appropriate for protocol and traffic statistics.
Active Network Monitoring Tools
Active network monitoring tools inject real packets into the network to measure end-to-end reachability, round-trip-time, packet loss, bandwidth, link utilization and other network proprieties. This type of network monitoring also tests applications from the user perspective and are also used for remote monitoring. A monitoring agent executes real transactions against an application, and then measures performance like execution and response time. This technique enables you to test the end result of network and applications, without having to monitor individual components and then inferring their availability and performance. The feedback and detection of network outages and performance degradation issues is much faster and more reliable.
Network Monitoring Tools Types: Quick Comparison
| Type | Primary Use | Limits |
|---|---|---|
| SNMP | Report the status and performance of network devices, such as routers and firewalls. | Doesn’t capture the end-user experience, but only the status and performance of network devices. |
| Passive | Capture traffic to identify network activity, apps performance, and security incidents. | Reactive network performance monitoring as it relies on real network traffic. |
| Active | Continuous synthetic monitoring to measure end-to-end performance and proactive alert of network issues. | Requires installation of a dedicated hardware or software monitoring agent. |
Evaluating Network Monitoring Tools
In general, when evaluating network monitoring tools, it’s important to list key requirements to compare different options. The comparison matrix will help determine which tool scores higher. Below we share some common requirements.
Real-Time
Consider how recent is the network monitoring data displayed. Does it take 5 seconds or 5 minutes for the dashboard to get the latest results?
Notifications and Integrations
What type of notifications does the tool support? What type of third-party applications does it integrate with, such as MS Teams, ServiceNow, etc.
Data Retention
The data retention will help determine the length of the historical data. What’s the storage requirement if hosted on-premises?
Scalability
How well does the tool scale? Does it meet your organization’s scale? How complex is the configuration to achieve that level?
Platform
Does the platform support my organization environment? Is it cloud only, or can it be hosted on-premises?
License and price
Consider if you prefer to opt for a commercial or an open source network monitoring tool, as each option has pros and cons. Consider not only the price, but also the cost to manage it and keep it updated.
Ease of use
How easy is it to use? Do I need specialized skills, or is it pretty self explanatory?
Active vs. Passive Tools
When thinking about Network Performance Management (NPM), what strategy should you prioritize? Should you go with an active network monitoring software, or a passive tool? The answer it depends form what the user wants to achieve. Most probably, an organization will need both systems to monitor their network, applications, and user experience. Let’s summarize what each one does.
Active monitoring takes an assertive approach by deploying hardware or software agents to run continuous network testing. The agents continually assess performance and detect potential issues preemptively, much like regularly checking your car’s tire pressure even without the warning light. On the contrary, passive monitoring tools observe and analyze the ongoing flow of network traffic to spot problems after they arise, resembling monitoring the speedometer for sudden spikes.
The choice between these approaches hinges on your requirements: active monitoring excels at pinpointing issues and guaranteeing SLAs, while passive monitoring provides insights into overall trends and identifies security threats. Ultimately, a combination of active and passive monitoring provides the most comprehensive understanding, ensuring a healthy network and satisfied users.
Cloud vs. On-Premises Tools
Another differentiation for network monitoring tools is whether they run on the cloud, on-premises, or hybrid.
On-premises network monitoring tools are typically installed and operated within an organization’s infrastructure, providing direct control over user access and data retention and residency. This traditional approach offers a higher level of customization and security but requires more maintenance.
On the other hand, cloud network monitoring tools are hosted and managed off-site by third-party providers, allowing for scalability and accessibility from anywhere with an internet connection. Generally cloud-based solutions often come with subscription models, reducing upfront costs and offering rapid scalability, making them particularly suitable for businesses with dynamic or growing network needs. The choice between these options depends on factors like security requirements, budget considerations, and the flexibility needed for network monitoring.
Network Monitoring with NetBeez
NetBeez is an active network monitoring platform that enables operations and support teams to quickly troubleshoot performance issues from the user’s perspective. NetBeez monitoring capabilities enable it to monitor:
- Websites, including SaaS, and hosted applications
- VoIP and videoconferencing (CCaaS, UCaaS) performance
- WAN, SD-WAN, WLAN, and cloud environments
- Internet path analysis to discover the network topology
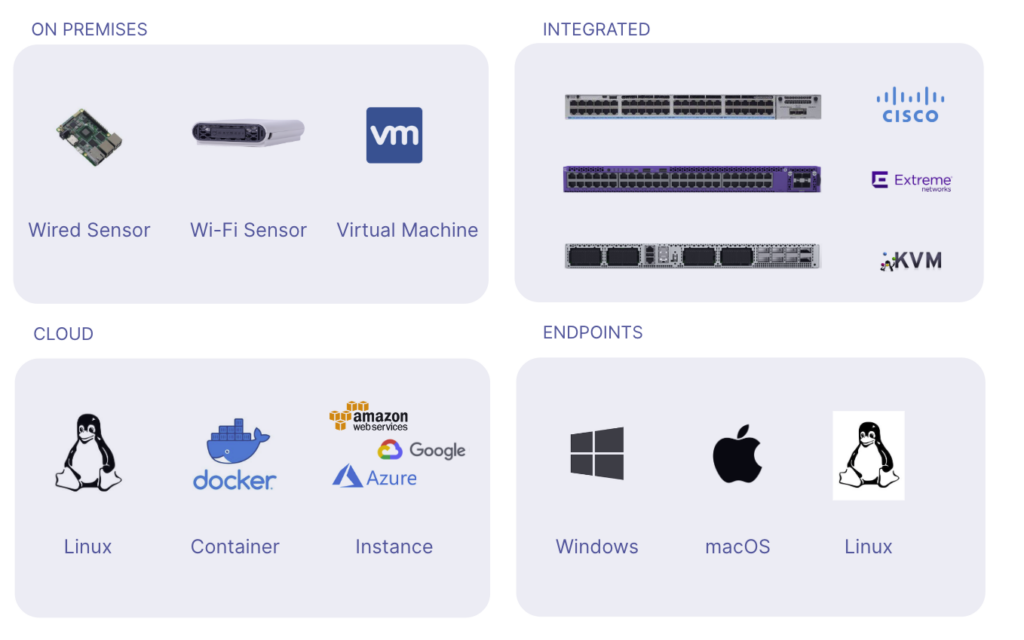
The solution relies on distributed network monitoring agents that provide end-to-end network and application performance metrics. NetBeez agents divide in two categories:
- Network Agents – Virtual, software, and hardware appliances that are installed on on-prem, on virtual environments, and cloud networks. The network agents include hardware wired and wireless units for LAN and WLAN monitoring or docker appliances for integrated monitoring.
- Remote Worker agents – Software clients for Windows, Mac, and Linux operating systems. They provide all the data necessary to monitor the digital experience of Work-From-Home employees.
NetBeez has three key pillars that make it a good solution for network troubleshooting.
Granular Performance Data
NetBeez captures granular network performance metrics to applications and services.
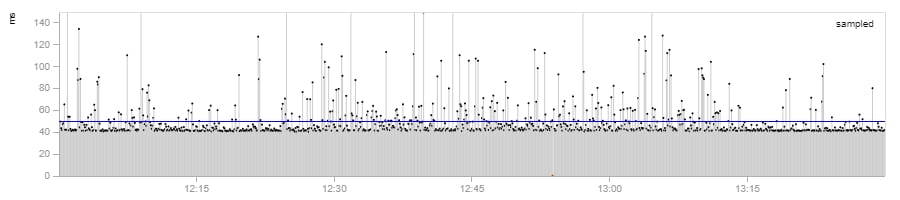
- Performance metrics up to one second interval, useful for monitoring WAN links
- Help isolate with accuracy the exact time and moment when a problem occurs
- Retains historical data to generate baselines, identify trends and recurring issues to perform root cause analysis
Proactive Incident Detection
NetBeez agents run real-time tests, end-to-end, and from the user perspective.
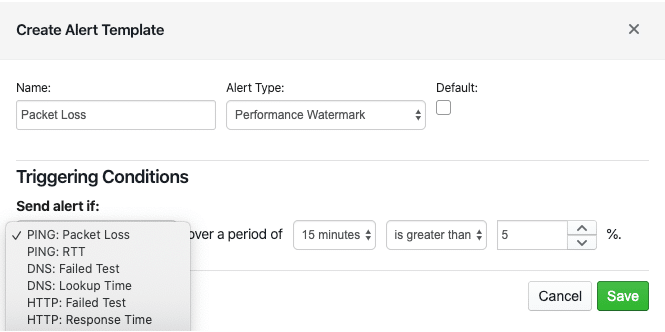
- Continuous active monitoring against networks and applications
- Quick detection and alerting on service failures and performance degradation
- Enforce and guarantee quality of service and SLAs
- Verify and validate configuration changes during maintenance windows
Multi-Platform Deployment
The solution supports flexible deployment options for on-prem, cloud, and remote.
- Deploy the server on-premises as a virtual appliance or in the cloud as an instance
- Support Ethernet, Wi-Fi, virtual, Docker, and Linux based agents
- Support Windows and Mac clients
- Easily orchestrate and deploy at scale
Request a free trial now.
How to Deploy NetBeez Network Monitoring
NetBeez provides a simple and effective way to monitor networks from the end-user perspective. NetBeez is an active network monitoring solution. It offers easy-to-deploy network agents and software clients to match the needs of organizations with a distributed workforce. If you want to learn more about NetBeez monitoring capabilities, request a demo or start a free trial.
Step1: Deploy network agents in private and public networks
The Network Agents are hardware (Wi-Fi or Ethernet), virtual, or docker appliances. They are deployed in private and public networks to continuously monitor network availability and performance. We recommend the installation of one or more hardware or virtual appliances at each branch office, data center, and headquarters. This way, NetBeez will ensure constant monitoring of network services and applications across your private and public network.
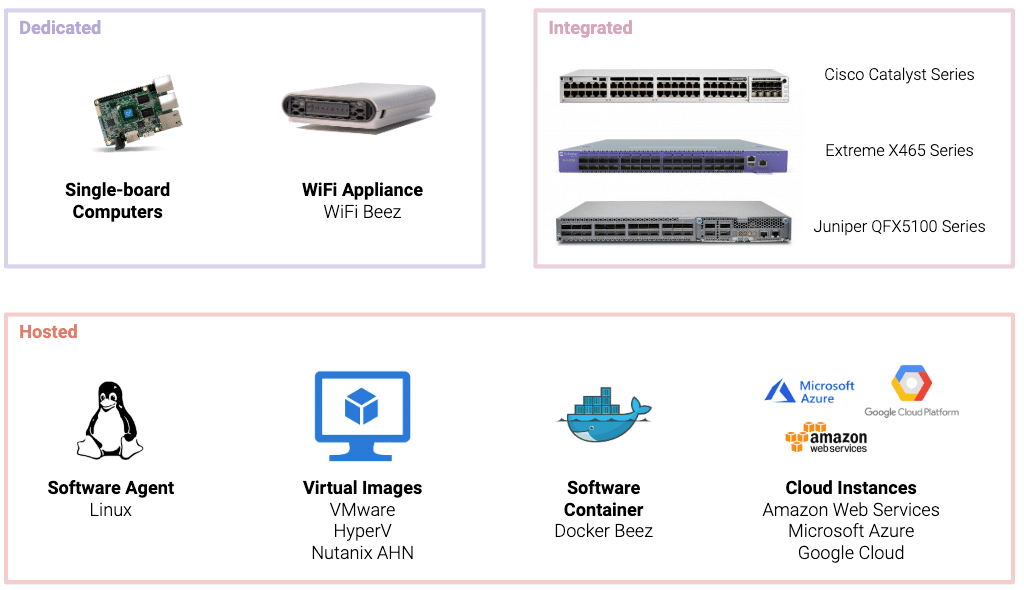
For organizations that need to monitor performance of cloud-based networks or applications, using cloud agents is essential. To have a comprehensive status of SaaS and cloud resources, we recommend to deploy three or more cloud agents . The agents verify availability and performance from public clouds like AWS, Azure, and Google. They will also collect information about outages occurring over the Internet.
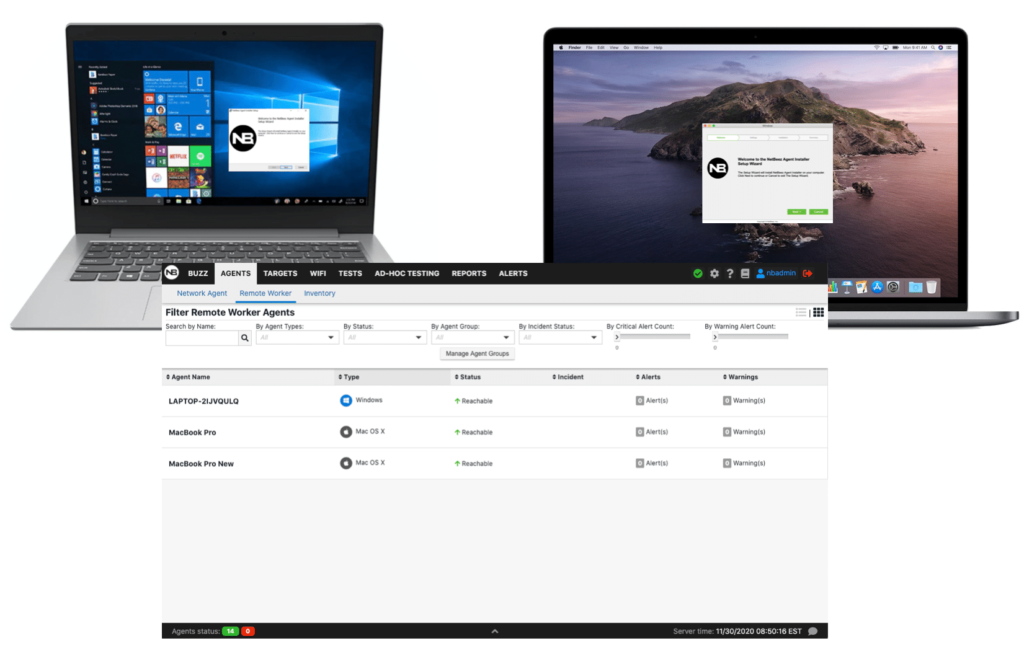
Step 2: Install remote worker agents for end-users
The Remote Workers Agents monitor and test a network availability and application performance from end-user perspective. These lightweight software clients are compatible with operating systems such as Windows, Mac OS, or iGel. They provide comprehensive performance data, including the status of the user’s wired and wireless network, internet speed, and endpoint performance. This method is particularly effective for quickly pinpointing the root cause of network or application issues encountered by remote users. By analyzing data from both network agents and remote worker agents, IT teams gain a thorough understanding of VoIP performance.
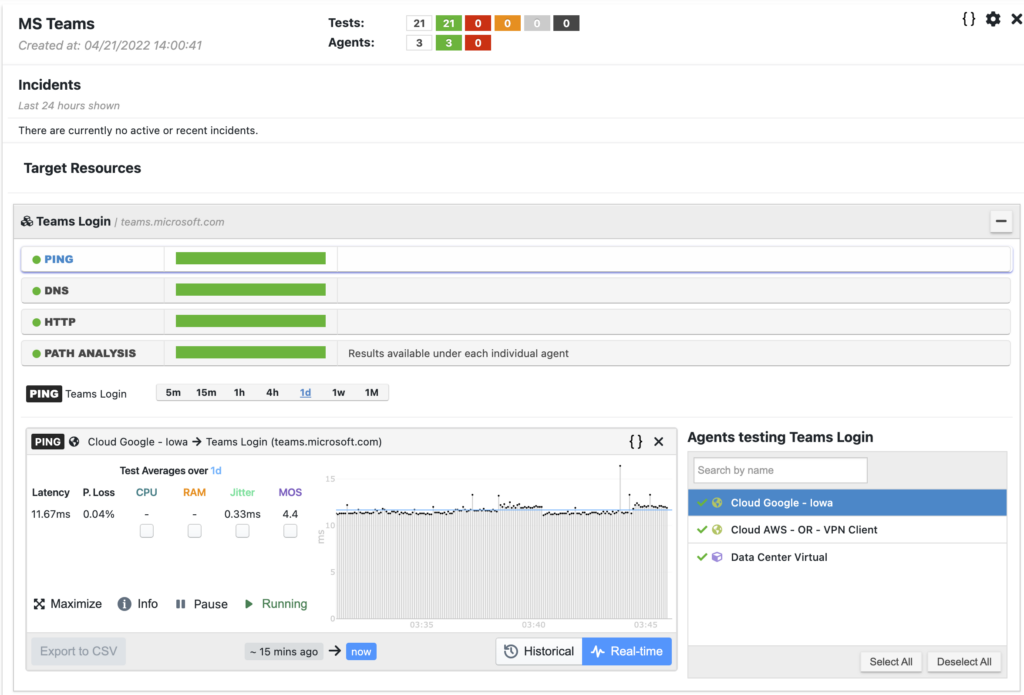
Step 3: Configure network monitoring targets and scheduled tests
Once the agents show up on the NetBeez dashboard, you can start monitoring the network and applications. NetBeez offers two complementary methods for network and application monitoring: targets and scheduled tests.
Targets are web or SaaS applications monitored via continuous network monitoring tests. These tests are ping, DNS, HTTP, traceroute and path analysis. They run at regular intervals, expressed in seconds. They provide real-time and historical performance data on internet connectivity, network topology, and more. Performance metrics such as latency, packet loss, DNS and HTTP response times are crucial for proactive detection of network problems. For example the following screenshot report a target to MS Teams.
Scheduled tests like iperf, speed test, and VoIP, provide network performance metrics such as download and upload speed against internet servers and cloud locations. These tests run according to a user-defined schedule, such as hourly or daily based on needs. In the following screenshot an iperf test reports throughput, packet loss, and jitter.

Conclusion on network monitoring tools
There are three types of network monitoring solutions available: SNMP-based, passive, and active. Each type of tools solves a specific network monitoring function. To successfully support today’s enterprise networks, network engineering teams should adopt a tool from each category. If you are looking for an active network monitoring solution that well integrates, try NetBeez by requesting a demo or starting a free trial. With NetBeez you can monitor your entire network, create custom dashboards if needed